Cybersecurity Imperatives for CMMS Development Companies.
The cybersecurity environment has grown more complicated and dangerous for software development companies in an era of unparalleled digital transformation.
This is particularly true for Computerized Maintenance Management System (CMMS) software providers, who hold the responsibility of safeguarding sensitive operational data and ensuring the integrity of mission-critical software systems.
CMMS software development companies need to be care of becoming so laser-focused on product innovation and feature enhancements that they inadvertently neglect the critical aspect of cybersecurity.
The alarming rise in sophisticated cyber threats underscores the urgent need to elevate cybersecurity as a top strategic priority.
This article aims to underscore the vital importance of implementing robust cybersecurity strategies within CMMS software development organizations.
By exploring the essential measures necessary to fortify digital infrastructure, we will equip readers with the knowledge and actionable recommendations to protect sensitive data, maintain operational integrity, and enhance overall resilience against malicious actors.
The key objectives of this article are:
1) To emphasize the critical role of cybersecurity in safeguarding CMMS software development companies and their clients in the digital age.
2) To provide a detailed overview of the most effective cybersecurity strategies and practices that CMMS software development firms can implement to mitigate risks and prevent costly breaches.
3) To offer practical guidance and industry-leading recommendations for establishing a comprehensive, multi-layered cybersecurity framework that addresses the evolving threat landscape.
4) To underscore the long-term benefits of investing in robust cybersecurity measures, including enhanced client trust, operational continuity, and competitive advantage in the marketplace.
I hope that after reading this article, readers will have a thorough understanding of the cybersecurity requirements that CMMS software development companies must meet.
Table Of Contents:
1.0 The Pivotal Role Of Cyber Security In Software Development.
2.0 Establish Real-Time Threat Detection Across Servers & Clouds.
3.0 Fortifying Internet Access with Robust Security Measures.
4.0 Achieving Complete Visibility and Effective Threat Identification.
5.0 A Multi-Layered Cybersecurity Defense Via A Recovery Vault.
6.0 Centralized Control and Efficient Threat Response.
7.0 Employee Training And Comprehensive Endpoint Security.
8.0 Mitigating Third-Party Cybersecurity Risks.
9.0 Incident Response and Business Continuity Planning.
10.0 Conclusion: Investing in Cyber Security for a Secure Future.
1.0 The Pivotal Role Of Cyber Security In Software Development.
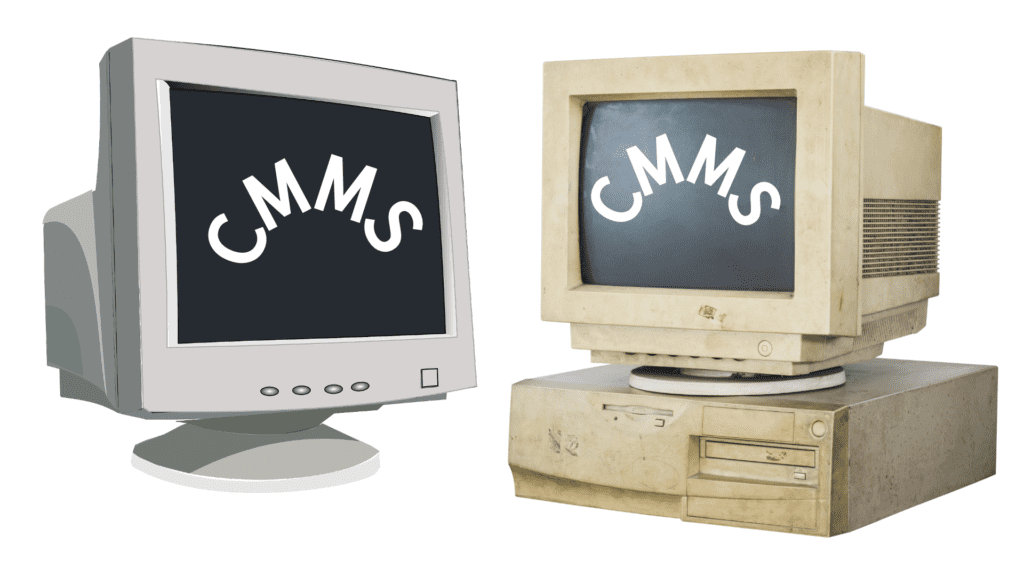
The integration of comprehensive cybersecurity strategies has become paramount for software development companies, particularly those focused on Computerized Maintenance Management System (CMMS) solutions.
While the primary emphasis is often on product innovation, feature enhancements, and meeting client demands, neglecting cybersecurity can lead to severe and far-reaching consequences that threaten the very sustainability and reputation of these organizations.
The stakes have never been higher. Cybercriminals have become increasingly sophisticated in their tactics, targeting software development companies with a range of malicious attacks aimed at compromising sensitive data, disrupting operations, and siphoning valuable intellectual property.
For CMMS software providers, the ramifications of a successful cyber attack can be devastating, spanning operational downtime, delayed product releases, substantial financial losses, and escalating insurance costs.
Robust cybersecurity measures are not merely an additional layer of protection – they are a fundamental component that ensures the smooth and reliable execution of CMMS software development and deployment.
By embedding rigorous security protocols into the development lifecycle from the outset, companies can identify and mitigate vulnerabilities early, preventing breaches that could compromise proprietary information and client data.
Protecting intellectual property is especially crucial within the highly competitive software development landscape.
Operational disruptions caused by cyber-attacks can significantly impact the development process, resulting in missed deadlines and hindering the company’s ability to deliver products on time.
For clients relying on these CMMS solutions, such delays can erode trust, leading to lost business opportunities and a damaged reputation in the marketplace.
The financial implications of cybersecurity breaches are multifaceted, ranging from direct costs such as regulatory fines, legal fees, and reparations to affected clients, to indirect costs that can be even more damaging, such as the loss of client confidence and the substantial expense of overhauling infrastructure to prevent future attacks.
The necessity for comprehensive cyber insurance policies becomes evident, yet these often come with significant premiums, further increasing operational costs.
Implementing stringent cybersecurity measures is an essential investment for CMMS software development companies aspiring for long-term success and sustainability.
Beyond simply averting immediate threats, these measures contribute significantly to operational resilience, client satisfaction, and financial prudence, positioning the organization as a reliable and forward-thinking player in the digital age.
2.0 Establish Real-Time Threat Detection Across Servers & Clouds.
CMMS development companies need to give top priority to the deployment of sophisticated and ongoing threat detection mechanisms on all servers and cloud environments, given the constantly changing and highly sophisticated nature of the cyber threat landscape.
This proactive approach enables organizations to identify potential threats in real-time, mitigating risks before they can cause significant damage and disruption to critical operations.
Adopting a comprehensive runtime threat detection strategy is an indispensable component of a robust cybersecurity framework.
Advanced threat detection systems leverage a powerful combination of machine learning, artificial intelligence, and behavioral analytics to monitor and analyze activities across both on-premise servers and cloud-based infrastructure.
By closely examining unusual patterns, anomalies, and suspicious behaviors, these systems can quickly identify and flag potential signs of malicious activity, allowing for swift and targeted response.
Integrating threat detection capabilities across diverse infrastructure layouts, including both local servers and cloud environments, ensures comprehensive coverage and eliminates potential vulnerabilities that could be exploited by cyber adversaries.
This dual approach to data and activity inspection enhances the overall security posture, providing a cohesive and extensive monitoring system that reduces the likelihood of exploitable gaps in the organization’s defense.
Moreover, the ability to seamlessly switch between local and cloud-based data analysis further strengthens the security measures, allowing security teams to adapt and respond to evolving threats with agility.
Real-time threat detection and response capabilities are essential for preventing data breaches, unauthorized access, and other types of cyberattacks that could compromise the integrity and security of the CMMS software development and operational processes.
Investing in and regularly updating state-of-the-art runtime threat detection tools is a strategic move for CMMS software development companies.
It not only safeguards sensitive data and intellectual property but also enhances the trust and confidence of clients and stakeholders in the organization’s commitment to cybersecurity.
To secure long-term success and preserve a competitive edge in the market, staying ahead of the curve with creative and dynamic threat detection solutions is not an option in this age of constant cyberattacks.
Maintaining a competitive edge through inventive and adaptable threat detection solutions is not merely a choice, but a must.
3.0 Fortifying Internet Access with Robust Security Measures.
Establishing and maintaining robust, secure internet access is the cornerstone of any comprehensive cybersecurity framework for Computerized Maintenance Management System (CMMS) software development companies.
In the face of the escalating threat of cyber-attacks, implementing multiple layers of security measures to protect internet-facing systems and data has become an essential imperative for these organizations.
The first line of defense lies in the deployment of advanced, enterprise-grade firewalls.
Firewalls serve as a critical barrier between a company’s internal network and external threats, filtering out malicious traffic while permitting legitimate communications.
By leveraging the latest firewall technologies, CMMS software development companies can recognize and proactively block unauthorized access attempts, safeguarding sensitive data and vital infrastructure from potential breaches.
Beyond firewalls, regular and comprehensive network monitoring is a crucial component of ensuring strong, secure internet access.
Continuous monitoring and analysis of network activities enable the real-time detection of suspicious behaviors and potential security incidents.
By employing sophisticated network monitoring tools and techniques, companies can swiftly identify anomalies and respond to threats before they can cause significant damage, minimizing the risk of extensive compromise.
Furthermore, the implementation of the latest security protocols is essential for preventing unauthorized access and securing internet-based communications.
Protocols such as Secure Sockets Layer (SSL) and Transport Layer Security (TLS) provide robust encryption for data transmissions, making it significantly more challenging for cybercriminals to intercept and exploit sensitive information.
Regular updates and maintenance of these protocols are necessary to keep pace with evolving cyber threats, ensuring that the highest security standards are consistently maintained.
Establishing and maintaining strong, secure internet access is a fundamental prerequisite for CMMS software development companies to protect against the ever-increasing landscape of cyber threats.
By implementing robust firewalls, engaging in comprehensive network monitoring, and leveraging the most current security protocols, these organizations can build a formidable defense against potential cyber-attacks, safeguarding their operations and maintaining the integrity of their critical systems and software solutions.
4.0 Achieving Complete Visibility and Effective Threat Identification.
Attaining complete visibility and employing efficient threat identification mechanisms is a critical pillar of a robust cybersecurity framework for Computerized Maintenance Management System (CMMS) software development companies.
This comprehensive approach ensures that every potential attack vector is closely monitored and managed, significantly enhancing the organization’s ability to detect and neutralize threats before they can cause substantial harm.
One highly effective strategy to achieve full visibility and control is through the strategic implementation of network segmentation.
By dividing the network into smaller, more manageable and isolated segments, companies can significantly limit the scope and impact of any single cyber attack, containing potential damage and preventing the lateral spread of threats.
Network segmentation allows for more granular monitoring and control, making it easier to identify anomalies that may indicate a security breach or ongoing malicious activity.
Complementing network segmentation, the adoption of state-of-the-art real-time monitoring tools is essential for comprehensive threat identification.
These advanced solutions leverage sophisticated algorithms and machine learning capabilities to continuously monitor network activities, system behaviors, and data flows, distinguishing between normal operations and potential security threats.
By automating the detection of suspicious activities, these tools enable swift countermeasures, preventing threats from escalating and causing substantial harm.
Regular vulnerability assessments are another indispensable component of maintaining complete visibility and effective threat identification.
These comprehensive evaluations help uncover weaknesses in the system that could be exploited by cybercriminals, including vulnerabilities in software code, network configurations, and even potential human vulnerabilities through social engineering tests.
The insights gained from these assessments guide the fine-tuning of security measures, enhancing the overall resilience against emerging threats.
In addition to the above strategies, establishing a centralized logging and reporting system is crucial for achieving a holistic view of the organization’s security posture.
Aggregating logs from various system components and network devices into a unified platform provides security teams with a comprehensive understanding of operational activities and patterns.
This visibility enables the analysis of potential threats, the identification of anomalies, and the generation of actionable intelligence to drive more informed and targeted security responses.
By integrating these methods – network segmentation, real-time monitoring, vulnerability assessments, and centralized logging, CMMS software development companies can achieve the level of visibility and threat identification necessary to safeguard their critical infrastructure and sensitive data.
With a comprehensive understanding of their attack surface and the ability to rapidly detect and respond to emerging threats, these organizations can better position themselves to mitigate risks and maintain operational resilience in the face of increasingly sophisticated cyber challenges.
5.0 A Multi-Layered Cybersecurity Defense Via A Recovery Vault.
To protect their digital assets and guarantee operational continuity, CMMS development companies need to implement a strong defense strategy that is multi-layered and adaptable to the ever-changing landscape of sophisticated cyber threats.
At the core of this comprehensive approach lies the integration of a specialized Cyber Recovery Vault, a critical component that provides an additional layer of protection for mission-critical data and systems.
The Cyber Recovery Vault is designed to segregate and isolate sensitive and business-critical data from common attack vectors, significantly reducing the risk of exposure to cyber adversaries.
By physically and logically isolating this vital data, the Cyber Recovery Vault helps maintain the integrity and continuity of essential operations, even in the event of a successful cyber attack.
The architecture of the Cyber Recovery Vault incorporates advanced cyber recovery software that fortifies it against unauthorized access and tampering. Central to its functionality are sophisticated synchronization capabilities that ensure continuous alignment of the stored data with the live operational environment.
This real-time synchronization is crucial for maintaining up-to-date backups, minimizing data loss, and facilitating swift recovery in the event of a security incident or system failure.
Complementing the secure data storage and recovery features, the Cyber Recovery Vault also employs tamper-proof mechanisms to enhance its overall security posture. These mechanisms prevent malicious modifications and unauthorized interventions, further safeguarding the sensitive information entrusted to the vault.
This level of protection is particularly vital for CMMS software development companies, which handle extensive and often mission-critical datasets, including proprietary intellectual property and client operational intelligence.
By implementing a multi-layered defense strategy that includes a well-protected Cyber Recovery Vault, CMMS software development companies can establish a resilient and comprehensive cybersecurity framework.
This approach not only helps prevent cyber incidents from occurring but also ensures rapid recovery and business continuity when necessary, maintaining operational integrity and preserving the trust of clients and stakeholders in an increasingly interconnected digital landscape.
6.0 Centralized Control and Efficient Threat Response.
To ensure a strong security posture in CMMS development companies, centralised control and effective threat response mechanisms are critical in the face of increasingly complex and sophisticated cyber threats.
This strategic approach enables organizations to consolidate and unify their security measures, ensuring consistency and thoroughness in the enforcement of policies across diverse systems, infrastructures, and operational environments.
A centralized control system enhances the efficiency and effectiveness of threat investigation and response.
By aggregating data from various network nodes, endpoints, and security tools into a single, integrated management console, security teams can quickly correlate events, identify patterns, and prioritize their response efforts.
This unified visibility is instrumental in detecting anomalies that may indicate a potential cyber attack, allowing for a rapid and coordinated defense against emerging threats.
Sophisticated security terminals play a crucial role in this centralized control environment.
Equipped with advanced auto-detection capabilities, these terminals leverage machine learning and artificial intelligence to continuously monitor activities, autonomously identifying and flagging suspicious behaviors in real-time.
This proactive approach significantly reduces the time required to detect and respond to threats, preventing them from escalating into more significant incidents.
Moreover, the remote response mechanisms integrated into these advanced terminals enable security personnel to neutralize threats without the need for onsite intervention.
This not only minimizes response times but also ensures efficient and effective threat management, preventing the propagation of attacks and maintaining the integrity of critical systems and data.
By integrating centralized control and efficient threat response mechanisms into their operational framework, CMMS software development companies can create a more resilient and secure IT environment.
These organisations can maintain seamless security operations by harmonising security practices, automating detections, and providing robust remote response capabilities, fortifying their defences against cyber threats and ensuring the dependability and trustworthiness of their software solutions, which is critical in building and maintaining client confidence in an increasingly connected world.
7.0 Employee Training And Comprehensive Endpoint Security.
For CMMS development companies, establishing a robust cybersecurity framework requires a two-pronged approach: investing in comprehensive employee training and implementing advanced endpoint security measures.
By empowering the workforce with the necessary knowledge and skills, while simultaneously fortifying the security of every device and access point, these organizations can create a multi-layered defense that effectively mitigates the risk of cyber threats.
Cyber security awareness training is a fundamental component of this strategy, ensuring that all employees are equipped to recognize and respond to common attack vectors, such as phishing, malware, and social engineering tactics. An informed workforce serves as a vital first line of defense, capable of identifying and reporting potential threats before they can escalate and compromise the organization’s systems and data.
This foundational knowledge lays the groundwork for more specialized and technical security training.
Beyond basic awareness, CMMS software development companies must also invest in cyber security engineering training, equipping their employees with technical skills to design, implement, and maintain secure systems.
This includes instruction on secure coding practices, understanding security architecture, and conducting rigorous system testing to identify and address vulnerabilities.
By fostering a culture of security-first development, companies can create CMMS software that is inherently more resilient to cyber threats.
Cryptography training is another essential element, empowering employees to understand and apply robust encryption techniques to protect sensitive data.
Knowledge of cryptographic algorithms, key management, and secure communication protocols is crucial for ensuring the confidentiality and integrity of information as it traverses the organization’s digital ecosystem.
Lastly, training in cyber security analysis sharpens the skills of employees to monitor, detect, and respond to potential security incidents.
By equipping personnel with the ability to analyze network activities, system behaviors, and log data, companies can enhance their threat detection and incident response capabilities, reducing the likelihood of successful cyber attacks.
Alongside comprehensive employee training, CMMS software development companies must also prioritize the implementation of advanced endpoint security measures.
This includes deploying robust antivirus and anti-malware solutions, implementing strong access controls and multi-factor authentication, and regularly patching and updating all devices connected to the network.
By securing every endpoint, organizations can minimize the attack surface and prevent unauthorized access or the introduction of malicious elements into their digital infrastructure.
By empowering employees through cybersecurity training and fortifying endpoint security, CMMS software development companies can create a multi-layered defense that effectively mitigates the risk of cyber threats.
This holistic approach, combining a security-aware workforce and a hardened technical environment, is essential for protecting sensitive data, maintaining operational integrity, and preserving the trust of clients in an increasingly perilous cyber landscape.
8.0 Mitigating Third-Party Cybersecurity Risks.
As CMMS development companies increasingly rely on a network of third-party vendors, partners, and cloud service providers, the need for robust third-party risk management has become paramount.
Cybercriminals often seek to exploit vulnerabilities in these external connections as a means of infiltrating the primary organization, making it essential for CMMS companies to extend their security controls and oversight beyond their own internal infrastructure.
Effective third-party risk management begins with a comprehensive vendor assessment and onboarding process.
CMMS companies must thoroughly vet the security posture of prospective partners, evaluating their cybersecurity practices, access controls, incident response plans, and compliance with industry standards and regulations.
This due diligence helps identify potential vulnerabilities that could be inherited through the third-party relationship.
Contractual agreements with third-party providers must include stringent security requirements and clear delineation of roles, responsibilities, and accountability.
Service-level agreements (SLAs) should stipulate security standards, data protection measures, breach notification protocols, and the right to audit the vendor’s security controls.
By establishing these contractual safeguards, CMMS companies can hold their partners accountable and maintain a level of control over the security of shared data and systems.
Ongoing monitoring and assessment of third-party cybersecurity practices are crucial for maintaining a robust risk management program. CMMS companies should regularly review vendor security postures, conduct periodic audits, and monitor for any changes or emerging threats that could impact the integrity of the partnership.
Implementing automated tools to continuously assess third-party risk can provide real-time visibility and enable proactive mitigation of potential vulnerabilities.
In the event of a third-party security incident, CMMS companies must have clearly defined incident response and communication protocols in place. These plans should outline the steps for quickly isolating the impact, notifying affected stakeholders, and coordinating recovery efforts with the third-party provider.
Regular testing and updating of these incident response procedures ensure the organization’s ability to swiftly and effectively manage disruptions originating from external sources.
By adopting a comprehensive third-party risk management approach, CMMS software development companies can extend their cybersecurity defenses beyond their own infrastructure, mitigating the risks posed by vendors, partners, and cloud service providers.
This holistic strategy helps safeguard sensitive data, maintain operational continuity, and preserve the trust of clients in an increasingly interconnected digital landscape.
9.0 Incident Response and Business Continuity Planning.
The creation of thorough incident response and business continuity planning frameworks must be given top priority by CMMS development companies in light of the dynamic and complex cyber threat landscape.
These critical components work in tandem to ensure the organization’s ability to swiftly detect, respond to, and recover from security incidents, ultimately safeguarding the integrity of their operations and maintaining the trust of their clients.
Incident response planning is the cornerstone of an effective cybersecurity strategy. CMMS companies must develop and regularly test detailed incident response procedures that outline the steps to be taken in the event of a security breach or cyber attack.
This includes clearly defined communication protocols, roles and responsibilities, and the necessary actions for containing the incident, mitigating its impact, and restoring normal operations.
Key elements of a robust incident response plan include:
1) Threat and vulnerability monitoring to enable early detection of anomalies.
2) Incident classification and escalation procedures.
3) Containment and eradication strategies to limit the spread of threats.
4) Forensic data collection and evidence preservation for investigation.
5) Seamless communication with internal stakeholders and external authorities.
6) Comprehensive recovery and restoration processes to resume operations.
Complementing incident response, business continuity planning ensures that CMMS software development companies can maintain critical functions and rapidly recover from disruptive events, whether they are caused by cyber incidents or other types of disruptions.
This involves identifying the organization’s most essential services, systems, and data, and implementing strategies to protect and restore them in the event of an emergency.
Effective business continuity planning includes:
1. Comprehensive data backup and recovery mechanisms.
2. Secure and accessible off-site storage of critical information.
3. Alternative communication and collaboration channels.
4. Redundancy in key infrastructure and systems.
5. Detailed procedures for activating and transitioning to backup operations.
6. Regular testing and updating of the business continuity plan.
By integrating robust incident response and business continuity planning, CMMS software development companies can establish a strong foundation of organizational resilience.
This dual-pronged approach enables them to swiftly detect and respond to security incidents, while also ensuring the uninterrupted availability of essential services and the timely restoration of normal operations.
Investing in these critical capabilities not only safeguards the company’s digital assets and intellectual property but also reinforces client trust, regulatory compliance, and the overall sustainability of the CMMS software development business in an increasingly volatile and unpredictable cyber landscape.
10.0 Conclusion: Investing in Cyber Security for a Secure Future.
Investing in a comprehensive cybersecurity strategy is an imperative for Computerized Maintenance Management System (CMMS) software development companies operating in the digital age.
As this document has extensively outlined, the cybersecurity landscape has become increasingly complex, with sophisticated threats targeting organizations across all industries.
By implementing a multi-layered defense approach, CMMS companies can safeguard their sensitive data, protect intellectual property, and ensure the long-term reliability and integrity of their software solutions.
This holistic cybersecurity framework must address a wide range of critical elements, from real-time threat detection and secure internet access to centralized control and employee training.
Equally important is the need to effectively manage third-party risks and establish robust incident response and business continuity plans.
CMMS companies must extend their security oversight to include vendors, partners, and cloud service providers, while also preparing for the eventuality of security incidents through clearly defined recovery procedures and continuity strategies.
By consistently investing in advanced cybersecurity measures, CMMS software development companies can not only mitigate risks and prevent costly breaches, but also build trust with clients, enhance their reputation, and position themselves as industry leaders in an increasingly interconnected and digitalized world.
The future of CMMS software development hinges on an unwavering commitment to cybersecurity.
As the threat landscape continues to evolve, organizations that prioritize the implementation of comprehensive security strategies will be better equipped to navigate the challenges, seize new opportunities, and thrive in the years to come.





[…] Equipment Servicing Information – CMMS SUCCESS. Insurance for CMMS software development companies. Cyber Security for CMMS Software Development Companies. Asset Management Training for Planners – CMMS SUCCESS. Your boss needs solutions not problems – […]
[…] Cyber Security Measures are paramount to protect sensitive data. Verify that the CMMS offers strong security protocols and data encryption. […]
[…] Furthermore, ensuring robust security measures to protect sensitive data from increasingly sophisticated cyber threats is non-negotiable. It’s probably worth checking out: Cyber Security For CMMS Development Companies – CMMS Success […]